We get so focused on cyberattack these days that it’s easy to forget how many risks to your personal info take place in the real...
Anatomy of a Phishing Scam
Recently some hackers grew sloppy and exposed their tactics and results of a major phishing campaign....
10 Tips: Protect Seniors from Online Fraud
Millions of our aging senior population fall prey to scams, fraud, and identity theft every year. Because older adults are more trusting and often are...
Data Breaches: A Ticking Time Bomb for Consumers
The impact of corporate breaches is becoming more widespread than ever, with ramifications spreading far beyond victimized companies to hit consumers and their families—often months...
Rethinking Passwords in the ‘Brute Force’ Age
Here’s a discomfiting thought: Experts say that even if you create a solid password with numerals and special characters, it can be cracked in eight...
The 7 Key Categories of Threat Actors
In cybersecurity, the term “threat actor” might refer to lone agents, organized criminal groups, or entire entities seeking to impact your personal security or that...
4 Things Your Home Office Needs
Whether you’re a longtime work-at-home veteran or a COVID newbie, here are some key elements of a secure home office...
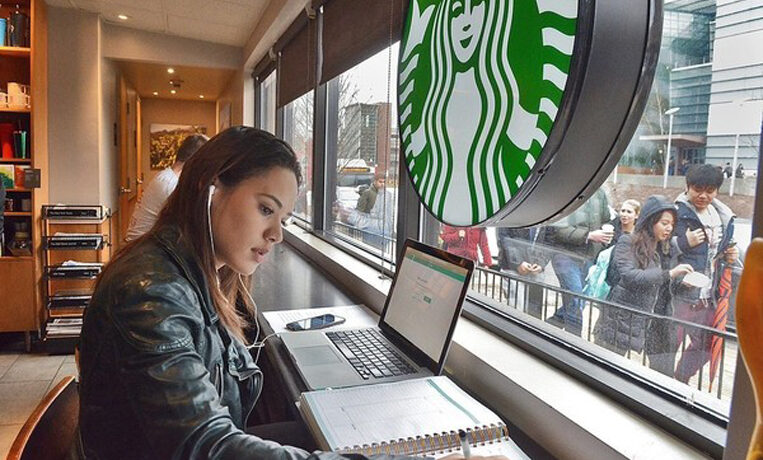
Starbucks Safety: Security Tips for Public Computing
Millions of workers, cooped up at home for nearly a year, are taking every opportunity to escape the house. Take a couple precautions with you...
Data Security: Myth vs. Reality
In today’s world it seems people read and hear only what they already believe—even when it comes to security. How else to explain all the...
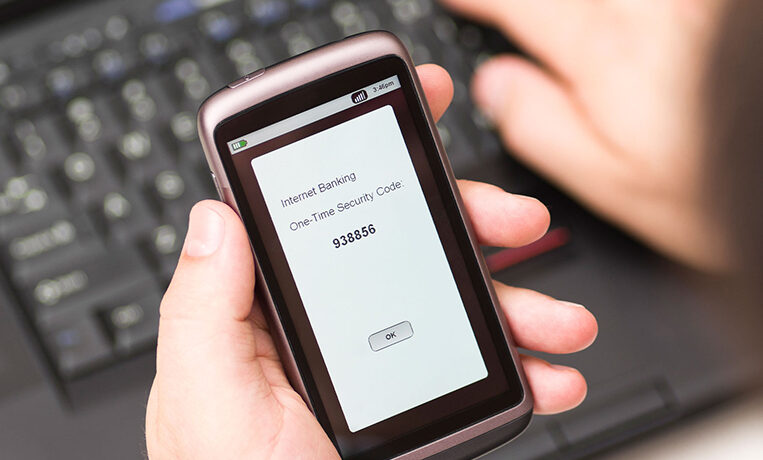
2FA: 6 Places to Start
These days, most people have at least some familiarity with two-factor authentication (2FA). For example, your ATM card uses 2FA. Here are 6 other places...